Security failures in pharmaceutical logistics are not just operational setbacks. They are patient safety events. When a shipment of temperature-sensitive biologics is hijacked in transit or a counterfeit batch slips through an unsecured warehouse, the consequences reach far beyond balance sheets. For procurement and logistics managers operating across Southeast Asia, a region with fragmented regulations, high cargo theft exposure, and deep API dependency on external suppliers, the stakes are exceptionally high. This guide breaks down the real threats, explains how security connects to product integrity and compliance, and offers a practical framework for building a more resilient pharma supply chain.
Table of Contents
- Understanding the security landscape in pharma logistics
- How security preserves product integrity and patient safety
- Navigating regulatory requirements for secure pharma supply chains
- Advanced security frameworks: From physical to cyber and vendor risks
- Why over-focusing on compliance can backfire—and what to do instead
- Take the next step: Fortify your pharma supply chain with expert support
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Security prevents major losses | Strong security in pharma logistics stops theft, product tampering, and ensures patient safety. |
| Product integrity relies on controls | Cold chain and real-time monitoring safeguard high-value drugs from degradation and counterfeiting. |
| Compliance demands robust security | GDP, DSCSA, and other frameworks require tight security to avoid costly fines and supply chain disruptions. |
| Cyber and vendor risks are rising | Digital security is essential as cyberattacks and weak partners can compromise logistics operations. |
| Proactivity outperforms box-ticking | Real-world scenario testing and continual improvement beat compliance-only approaches for true supply chain resilience. |
Understanding the security landscape in pharma logistics
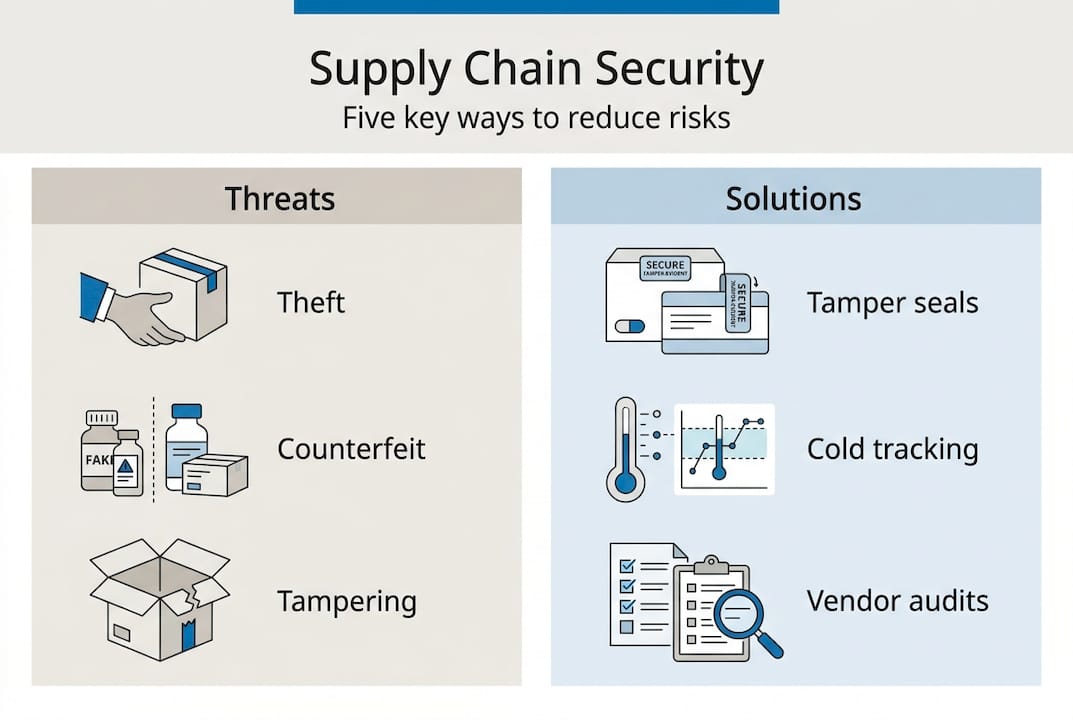
Security in pharma logistics covers four distinct threat categories: physical theft, product counterfeiting, tampering, and cyberattacks. Each one creates a different type of exposure, but all four can result in theft, counterfeiting, and tampering that puts patients at direct risk. Understanding where these threats concentrate is the first step toward managing them.
The numbers are sobering. In EMEA, €17.8M stolen in 30 days included pharmaceutical cargo as a significant share. In South Asia, approximately one full truckload is hijacked annually for every 10,000 shipments. Southeast Asia sits at a similar risk level, compounded by multi-country transit routes, inconsistent border controls, and a heavy reliance on third-party carriers.
One structural vulnerability that is often underestimated: approximately 97.7% of active pharmaceutical ingredients (APIs) used across Southeast Asia originate from China. This concentration creates a single-source dependency risk. Any disruption at the manufacturing or export level, whether from geopolitical friction, regulatory action, or logistics failure, cascades across the entire regional supply chain.
The main entry points for security disruption include:
- Transit corridors: Cross-border road and sea routes with limited real-time oversight
- Cold storage facilities: Points where temperature-sensitive products are most vulnerable to tampering or theft
- Digital infrastructure: Warehouse management systems, ERP platforms, and tracking software that are increasingly targeted by cybercriminals
- Vendor handoffs: Transitions between 3PL providers, freight forwarders, and last-mile carriers
| Threat type | Primary entry point | Potential impact |
|---|---|---|
| Physical theft | Transit, warehousing | Revenue loss, patient harm |
| Counterfeiting | Procurement, distribution | Brand damage, regulatory action |
| Tampering | Storage, last-mile delivery | Product degradation, liability |
| Cyberattack | IT systems, vendor networks | Data breach, shipment delays |
For a broader view of how these threats interact with operational realities, the key challenges in pharma logistics across the region provide important context. Brand reputation and patient safety are both directly tied to how well these entry points are controlled.
How security preserves product integrity and patient safety
Not all security risks carry the same weight. For pharmaceutical products, the most consequential failures are those that compromise product integrity at the molecular level. Temperature excursions during a hijacking or an unauthorized warehouse entry can render an entire shipment clinically ineffective or actively harmful.
The financial scale of this problem is significant. Temperature-sensitive drug degradation contributes to approximately $35 billion in annual global losses. Biologics, vaccines, and cell therapies are especially vulnerable, as many require continuous cold chain maintenance between 2°C and 8°C. A single breach, even a brief one, can compromise an entire pallet.
“Approximately 70% of leading pharmaceutical products require strict temperature control throughout the supply chain. A security failure is also a cold chain failure.”
The top integrity risks that procurement managers need to monitor include:
- Temperature deviation: Caused by power failures, improper handling, or delayed transit during security incidents
- Deliberate tampering: Repackaging or substitution of product during theft events
- Counterfeiting: Replacement of genuine product with substandard or falsified medicines
- Shipment delays: Extended transit times caused by security incidents that push products outside their stability window
| Product category | Temperature requirement | Security sensitivity |
|---|---|---|
| Biologics and vaccines | 2°C to 8°C | Very high |
| Oncology drugs | 15°C to 25°C | High |
| Generic oral solids | Ambient | Moderate |
| Blood-derived products | 2°C to 6°C | Very high |
For practical guidance on maintaining these standards under real-world conditions, cold chain management strategies specific to Southeast Asia are worth reviewing in detail.

Pro Tip: Deploy tamper-evident seals on all high-value shipments and pair them with real-time temperature and GPS monitoring. If a security incident occurs, you will have a precise record of when and where product integrity may have been compromised, which is essential for regulatory reporting and insurance claims.
Navigating regulatory requirements for secure pharma supply chains
Maintaining product integrity is only half the story. Security also serves as the operational backbone of regulatory compliance, and in Southeast Asia, that compliance landscape is anything but simple.
The primary frameworks that govern secure pharma distribution include the EU Good Distribution Practice (GDP) guidelines, the U.S. Drug Supply Chain Security Act (DSCSA), and WHO cGMP standards. GDP, DSCSA, and cGMP compliance requires end-to-end traceability, serialization, qualified supplier networks, and documented chain-of-custody records. All of these controls depend on robust physical and digital security.
At the national level, the regulatory patchwork across Southeast Asia adds significant complexity. Singapore’s Health Sciences Authority (HSA) processes product registrations in approximately 30 to 270 days depending on the regulatory pathway. Thailand’s Food and Drug Administration requires 180 to 540 days for similar approvals. Each country also maintains its own import licensing, labeling, and distribution authorization requirements.
The must-have compliance controls for a secure supply chain include:
- Serialization and track-and-trace: Unique product identifiers at the unit level to detect diversion or counterfeiting
- Chain-of-custody documentation: Verified handoff records at every transfer point
- Qualified supplier management: Formal vendor qualification and periodic re-auditing
- Temperature and condition monitoring: Continuous data logging with deviation alerts
- Incident reporting protocols: Documented procedures for security breaches that satisfy regulatory notification requirements
For a detailed overview of the regulatory risks in Southeast Asia and how they interact with logistics operations, the regional breakdown is instructive. Staying current on evolving requirements is equally important, and tracking regulatory updates for pharma logistics across the region should be a standing agenda item for your compliance team.
Pro Tip: Build a continuous training program that covers both your internal team and your 3PL partners. Regulatory environments in Southeast Asia shift frequently, and a vendor who was compliant last year may not meet current standards today.
Advanced security frameworks: From physical to cyber and vendor risks
With compliance as your backbone, you need an action plan that addresses the full spectrum of modern threats. Physical controls alone are no longer sufficient. The most sophisticated attacks on pharma supply chains today combine physical access with digital exploitation.
Cybersecurity risks in pharma logistics now represent a direct threat to shipment integrity, with breaches capable of disabling tracking systems, falsifying temperature records, and exposing sensitive shipment data to criminal networks. A third-party vendor with weak IT security is a vulnerability in your supply chain, regardless of how strong your own systems are.
A layered security framework built on end-to-end visibility using GPS, RFID, and IoT provides the most effective defense. Key components include:
- Real-time GPS tracking on all high-value shipments with geofencing alerts for route deviations
- 24/7 control tower monitoring with escalation protocols for anomalies
- Biometric access controls at warehouses and distribution centers
- Tamper-evident packaging with serialized seals that log opening events
- Vendor cyber audits that go beyond paper certifications to include active system testing
- Night-driving restrictions on high-value cargo routes, a measure that has demonstrably reduced hijacking incidents in several Southeast Asian markets
For inventory risk controls that integrate with these security measures, aligning your stock management systems with your security protocols creates a unified defense layer.
Pro Tip: Do not assume a vendor’s ISO or GDP certification means their cybersecurity is sound. Ask specifically about their incident response plan, data encryption standards, and how they handle third-party system access. A paper audit and a live system audit are very different things.
Why over-focusing on compliance can backfire—and what to do instead
Here is an uncomfortable truth that many procurement managers encounter only after a serious incident: organizations that treat security as a compliance exercise are often the most exposed. Checklists get completed. Certifications get filed. And then a driver takes an unauthorized route, a vendor’s system gets breached, or a warehouse staff member bypasses a protocol that seemed inconvenient. None of these failures show up in a compliance audit until after the damage is done.
The real measure of supply chain security is not whether your documentation is current. It is whether your team and your partners behave securely when no one is watching. That requires scenario testing, not just SOP reviews. It requires staff who understand why a protocol exists, not just how to follow it.
In Southeast Asia specifically, building resilience through multi-sourcing and local partnerships has proven more effective than relying on a single certified vendor. When one node in the network fails, whether from a regulatory hold, a cyber incident, or a physical disruption, a diversified partner network keeps product moving.
The question worth asking your team today: are you auditing your vendors’ actual cyber practices, or just reviewing their paperwork? For a sharper look at where operational gaps tend to hide, smart solutions in pharma logistics offers a practical starting point.
Take the next step: Fortify your pharma supply chain with expert support
If the risks outlined in this article feel familiar, that is a signal worth acting on. Labgistics Asia has spent over 20 years building logistics infrastructure specifically for pharmaceutical and life science companies operating across Southeast Asia.
From secure cold chain logistics and GDP-compliant warehousing to regulatory guidance and business support services that help you navigate product registration and market entry, we offer end-to-end solutions tailored to the region’s specific challenges. Whether you are assessing your current security posture or building a new distribution strategy, our team can help you identify gaps and implement controls that meet both local and international standards. Explore our full range of pharma logistics solutions to see how we can support your operations.
Frequently asked questions
What are the main threats to security in pharma logistics?
Theft, counterfeiting, and tampering are the primary physical threats, while cyberattacks targeting logistics systems represent a growing digital risk. Together, they can cause product loss, patient harm, and significant regulatory exposure.
How does security protect product integrity in pharma logistics?
Strong security prevents medicines from being degraded, diverted, or falsified during transit and storage. Temperature-sensitive biologics and vaccines are especially vulnerable, making physical and environmental controls inseparable from product quality.
Why is regulatory compliance linked to logistics security?
Most frameworks including GDP and DSCSA require serialization, traceability, and documented chain-of-custody records. GDP, DSCSA, and cGMP requirements can only be met consistently when robust security protocols are embedded throughout the supply chain.
What role does cybersecurity play in pharma logistics?
Cybersecurity risks in logistics include system breaches that disable tracking platforms, falsify condition records, and expose shipment data, all of which can delay life-saving medications and trigger regulatory investigations.
What is a best practice for reducing security risks in the supply chain?
Combining GPS, RFID, and IoT monitoring with regular vendor audits and ongoing staff training creates a layered defense that addresses physical, digital, and human risk factors simultaneously.
Recommended
- Pharma Logistics Challenges and Smart Solutions | Labgistics
- Green Cold Chain and Eco-Friendly Pharma Logistics | Labgistics
- How to validate medical logistics processes: 5 key steps
- Cold Chain Logistics for Pharma in Southeast Asia | Labgistics
- How to Prevent Cargo Theft: Secure Your Supply Chain – ORNER
